Privacy Policy Regarding Google APIs and Services
At asinzen, we take the privacy and security of our users’ data seriously.
The provided Functions, integrations, and addons for Google Workspace products are not provided by Google nor sponsored or affiliated with Google.
Privacy Policy Regarding Google Chrome Store Extensions
asinzen is compliant and adheres to the Google Chrome Developer Privacy Policy Terms and is compliant with the following terms:
- Does not handle any personal or sensitive user data.
- Does not contain any Ads
- Does not alter any data on any site visited.
- Does not store any personal data handled within extensions.
Privacy Policy Regarding Google Account Integrations For AZInsight Chrome Extension and ScanEZ mobile app
API Usage: Google Sheets
- When you use the AZInsight Chrome Extension and ScanEZ mobile app Google Integration, we do not store or use any of your data without your permission. Granting us access to your data does not allow us to access it offline.
- We only access the data necessary to perform the app’s functions and do not use it for any other purposes.
- Our Integration Platform enables us only to modify spreadsheets on your Google Drive. To provide you with this service, we obtain a copy of the user’s Google email account when this connection is made using the Google APIs. We will not use this information in any other way.
- We do process or investigate any issues regarding your Google Spreadsheets if required by you and only under your explicit permission and do not have access to any of the Data on your Google Account.
- We will never share your data with third parties.
No data is transferred or stored to any system outside of your Google Account. Your information will never be sold, shared, or leased.
Privacy Policy Regarding asinzen Insight Google Add-on
API Usage: Google Sheets
- When you use the asinzen Insight Add-on, we do not store or use any of your data without your permission. Granting us access to your data does not allow us to access it offline.
- We only access the data necessary to perform the add-on’s functions and do not use it for any other purposes.
- The data that you select in your Google Sheet is sent to asinzen Insight APIs as values using Amazon SP-Token updated and accurate ASIN information and always remains on Google servers
- We will never share your data with third parties.
No data is transferred or stored to any system outside of your Google Account. Your information will never be sold, shared, or leased.
This Add-on’s use and transfer to any other app of information received from Google APIs will adhere to the Google API Services User Data Policy, including the Limited Use requirements.
Your use of this add-on is subject to the Google APIs Terms of Service
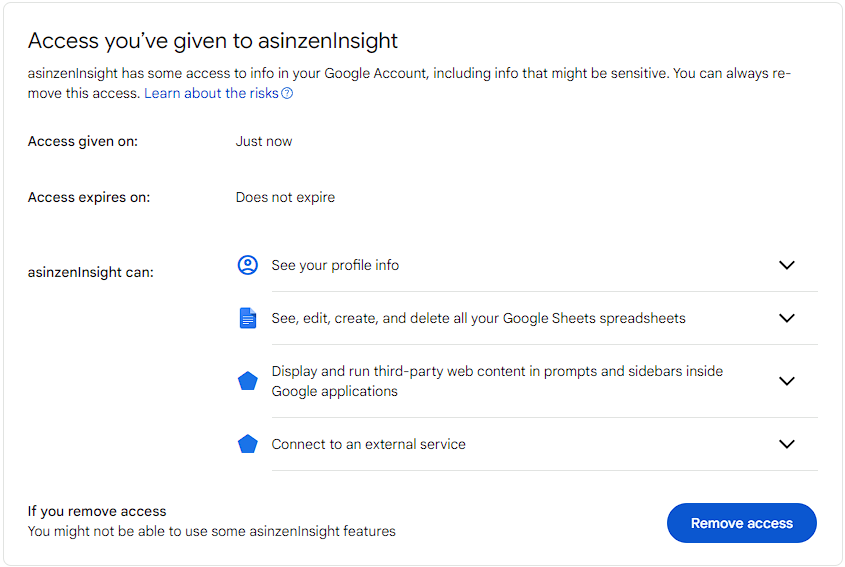
The add-on however requires the following permissions for it to operate:
- View and manage spreadsheets that this application has been installed in. This permission is required to read inputs from your selected sheet and write the result in your sheet. The add-on will NOT create or delete any spreadsheet files from your drive. Please note that the data in your sheet is NOT stored or shared with anyone for analysis or marketing.
- View and manage documents that this application has been installed in. This permission is required to read inputs from your selected document and write the result in your document.
- Connect to an external service: This scope is to request data from asinzen and Amazon’s APIs.
- Display and run third-party web content in prompts and sidebars inside Google applications. This permission is required to display a sidebar in your Google Sheet.
Here is a summary of how we use and protect your data:
- Data Collection: We only collect the data necessary to perform the functions of the asinzen Apps and services “AZInsight Chrome Extension, ScanEZ Mobile app, and asinzen Insight Google Add-on”. This includes the data in your active Google Sheets.
- Data Access: We only access your data with your explicit permission and only for the purposes of performing the functions of the “AZInsight Chrome Extension, ScanEZ Mobile app, and asinzen Insight Google Add-on”. We will never use your data for any other purposes or share it with third parties.
- Data Storage: We do not store any of your data on our servers or any other storage devices. All data is stored on Google’s servers and is subject to Google’s security and privacy policies.
- Data Security: We take all reasonable measures to protect your data from unauthorized access, theft, or loss. All data is transmitted over secure connections, and we use industry-standard security protocols to protect your data.
No data is transferred or stored to any system outside of your Google Account. Your information will never be sold, shared, or leased.
Revoking the permissions
To review the permissions granted to any of our Apps and Services “AZInsight Chrome Extension, ScanEZ Mobile app, and asinzen Insight Google Add-on”, please navigate to Google Account -> Third-party apps with account access -> Manage third-party access. You can review and remove access here.
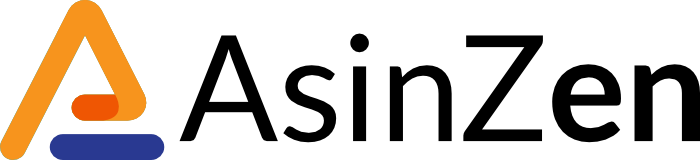
AZInsight Permissions
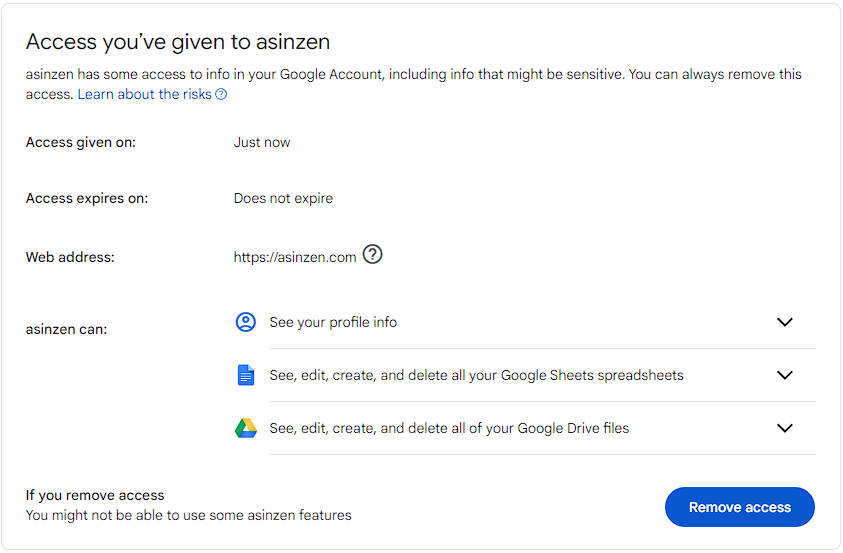
ScanEZ Permissions
asinzen Insight Google Add-on Permissions
How to Contact US
If you have any questions or concerns about this Privacy Policy or our privacy practices, you may contact us directly by email at: support@asinzen.com
If you are a resident of the European Union, and you believe that our processing of your Personal Information is inconsistent with your data protection rights under the GDPR and we have not adequately addressed your concerns, you have the right to lodge a complaint with the data protection supervisory authority of your country. http://ec.europa.eu/justice/data-protection/bodies/authorities/index_en.htm
EFFECTIVE DATE OF THIS PRIVACY POLICY
This Privacy Policy was last revised on May 17, 2025.